App Transport Security (ATS) could by bypassed with NSAllowsArbitraryLoads in the Info.plist for development, internal use and testing – however, since iOS 11.x this is no longer the case. Suddenly, your API and microservices stop working and the Xcode log is littered with tcp_timers tcp retransmit SYN errors, whereas it was working perfectly fine before – that’s the sign of the iOS kernel (XNU) marking the connection potentially insecure and preventing it from being successfully established.
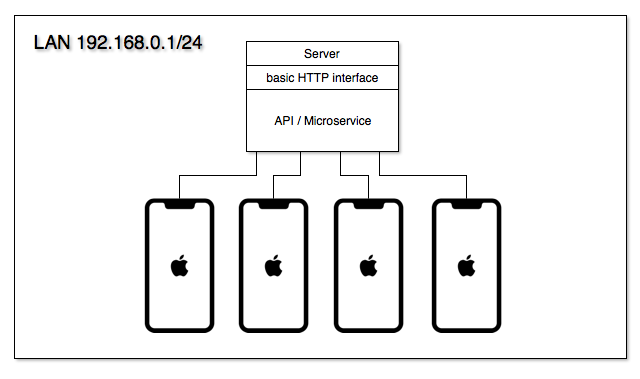
The LAN before time – a network without domain name resolution
Those of us using their interfaces through a properly certified SSL-enabled site remain unaffected by the above, but not so for anyone else who communicates within a private network isolated from the public internet with no means of employing a third-party certificate or even worse, can only use IPv4 or IPv6 addresses (due to the lack of domain name resolution). Consider the following basic scenario:
The main idea is to create certificates for our services and sign them via our master root SSL certificate authority – this way we will only need to install the root certificate on our test devices to enable access to all of the services that have their certificates signed by our root certificate authority, which is pretty neat!
Creating the root Certificate Authority
We’ll be using Apache 2 as the httpd server with the openssl package – although similar steps apply to any other alternative software. These commands are to be issued within a terminal session.
- Let’s create the root CA that will be used for signing. First, the keyfile:
openssl genrsa -out rootCA.key 2048 - Now for the actual root certificate:
openssl req -x509 -sha256 -new -key rootCA.key -out rootCA.cer -days 3650 -sub /CN="Root CA for iOS"
Installing the root CA on your iOS device
The rootCA.cer file can now be used on your iDevices: email them or put them on the local web server for easy access: just open them within the mail or in Safari and accept the dialogs, entering the device password when necessary.
After installing you must actually enable the root certificate on the iOS device (Apple Support article) in:
Settings > General > About > Certificate Trust Settings
without doing this step the communication will fail as if we did nothing – be sure to enable your cert.
Creating and signing the certificates for your server
Now for the certificate that will be installed on the server (repeat for the number of servers needed).
- Let’s create a private key for the server:
openssl genrsa -out server1.key 2048 - Now the CSR signing request for the server:
openssl req -new -out server1.req -key server1.key -sub /CN=192.168.0.1 - And lastly, we sign the request with our root CA from above:
openssl x509 -req -sha256 -in server1.req -out server1.cer -CAkey rootCA.key -CA rootCA.cer -days 3650 -CAcreateserial -CAserial serial - Install server1.cer and server1.key on your server and enable the SSL module
After this, all your iOS devices which have the rootCA installed on them will be able to once again communicate with the servers via HTTPS that have their certificates issued and signed as per above.